QUESTION 91
You work as an administrator at L2P.com. The L2P.com network consists of a single domain named L2P.com. All servers on the L2P.com network have Windows Server 2008 R2 installed. Some of L2P.com’s workstations have Windows 7 installed, while the rest have Windows 8 installed.
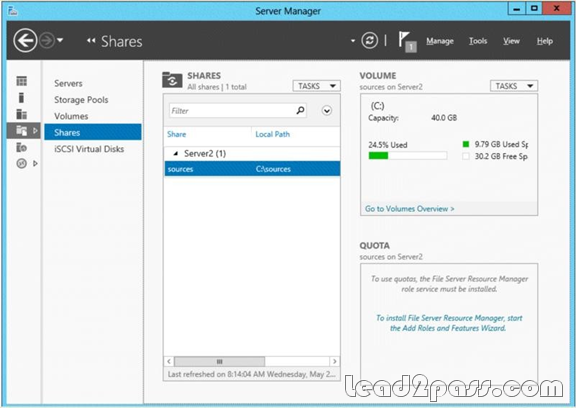
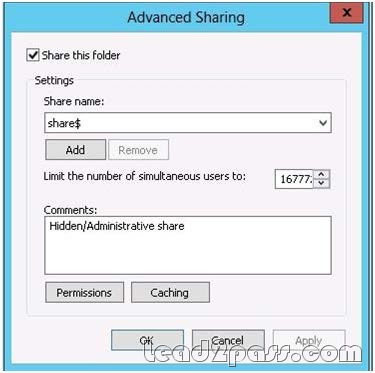
After installing a new Windows Server 2012 computer in the L2P.com domain, you configure it to run the File and Storage Services server role. You are instructed to create a shared folder on the new server, and configure the use of Previous Versions for restoring files located in the shared folder.
Which of the following actions should you take?
A. You should consider configuring the Shadow Copies settings on the new server.
B. You should consider configuring the Snapshot settings on the new server.
C. You should consider configuring the Background Copy settings on the new server.
D. You should consider configuring the Permission settings on the new server.
Answer: A
Explanation:
What are previous versions?
Previous versions are either backup copies (copies of files and folders that you back up by using the Back Up Files wizard, or shadow copies) copies of files and folders that Windows automatically saves as part of a restore point. (Shadow copies can be copies of files on your computer or shared files on acomputer on a network.) You can use previous versions of files to restore files that you accidentally modified or deleted, or that were damaged. Depending on the type of file or folder, you can open, save to a different location, or restore a previous version.
ATT: ( nothing to do with question but cool to know ) File Server Volume Copy Shadow Service (VSS) Agent Service Enables consistency of application snaphots (shadow copies). With previous versions of Windows Server, VSS only supported shadow copies of data on the local server. With WS2012, Microsoft has added VSS for SMB File Shares which extends shadow copy support for network volumes.Administrators install the FS VSS Agent on the file server where the application data is located. They then install the VSS provider in the server where the application is located. The provider talks to the agent using the new File Server Remote VSS protocol in order to manage the shadow copies of the data.
http://windows.microsoft.com/en-gb/windows-vista/previous-versions-of-files-frequently-asked-questions
» Read more
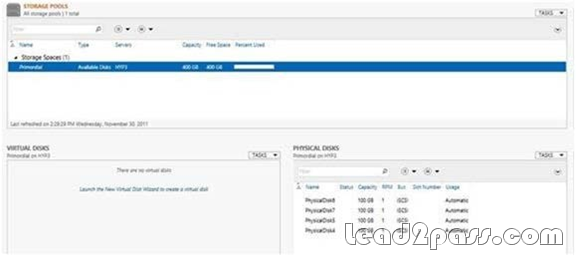
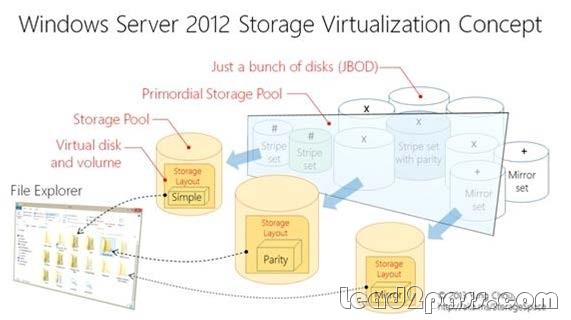 http://blogs.technet.com/b/canitpro/archive/2012/12/13/storage-pools-dive-right-in.aspx http://blogs.technet.com/b/askpfeplat/archive/2012/10/10/windows-server-2012-storagespaces-is-it-for-youcould-be.aspx
http://blogs.technet.com/b/canitpro/archive/2012/12/13/storage-pools-dive-right-in.aspx http://blogs.technet.com/b/askpfeplat/archive/2012/10/10/windows-server-2012-storagespaces-is-it-for-youcould-be.aspx